Privacy and the integrity of personal and corporate data is becoming one of the most significant areas of the digital world, driven by trends such as BYOD increasing the use of cloud computing in the corporate space, or the continuous use of social media in the consumer space. As online fraud, e-crime and many emergent threats move into the tablet and smartphone space, a solid commitment to offering products and services to protect customers and their digital lives becomes paramount for any self respecting Telco.
Welcome to the dire need for Identity Management ( IDM ). In a nutshell, IDM is an integrated system of business processes, policies, and technology that lets an organization control user access to online applications or services while protecting the user’s privacy and the organization’s resources.Telcos that undertake strong IDM service programs can capitalize on their existing assets to create additional revenue streams with subscriber identity data.
In 2012, the Edelman Trust Barometer indicated that distrust amongst consumers was growing; compared to just a year ago, twice as many countries surveyed are now skeptical and fewer countries are neutral. In fact, a privacy survey of 9,200 interviewees in 14 countries around the globe conducted by the research company Psychonomics reveals that custom¬ers are increasingly concerned about the use and misuse of their data. 82% of respondents see privacy as an important topic; 76% are concerned about privacy violations; and 45% of subscribers feel they lack control over their personal data. Only 9% of respondents don‘t care about data protection in general, whereas 80% of re¬spondents claim to be selective about sharing their personal data and why. A further 73% are afraid of their personal data being sold to third parties. In a digital age characterized by complex¬ity and concerns about privacy and security, customers are increasingly drawn to the idea of a Trusted Identity Provider.
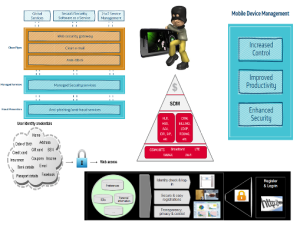
However, the major challenge that operators face in using their data to generate revenue, is that customer data is still siloed on legacy systems, due to their past merger and acquisition activity. Therefore, operator IT departments would need to invest in data integration, MDM ( Mobile Device Management ) , data quality tools and the necessary in-house expertise to use these tools effectively. If Telcos could leverage this subscriber data in real-time they can not only improve their service offerings, but can also create completely new revenue streams and support third parties in numerous industry sectors in improving their service offerings to their customers.
Before Telcos can become true and trusted identity providers, they need more than just authentication, authorization, and accounting (AAA) servers inside their networks; they also need directory servers, tools for managing subscriber access, and the federation software itself. Thats big investments but if the Tecos don’t do it the Web 2.0 players will do and capitalise on this huge IDM opportunity. Most executives compare the cash flows from innovation against the default scenario of doing nothing, assuming incorrectly that the present health of the company will persist indefinitely if the investment is not made. For a better assessment of an innovation’s value, the comparison should be between its projected discounted cash flow and the more likely scenario of a decline in performance in the absence of innovation investment.
Some Telcos may not really know yet how they will make money as an identity provider, but they are certain that IDM will help deliver services that can reduce customer churn. Fortunately proactive operators do see this opportunity and are acting on it. France Télécom – Orange is among a handful of European and Asian network operators that are implementing IDM technology and learning to become identity providers – companies that can, in effect, vouch for a user’s identity in transactions with Web-based service providers. In Argentina, operator MoviStar, is offering a single sign-on service. With one single password, the user can access to online services such as Facebook, Twitter and Flickr moving to “zero sign on”, with all a customer’s identities stored on the secure element of the SIM card.
Telfonica has segmented its Security market under Information Security , Electronic security and Mobile Security mapped across Consumer / SME and Enterprise / Gov sectors and sales estimated at $ 300 million. Their Enterprise security solutions include Web security gateway ( secure internet surfing ) , Clean e-mail ( mail security service ) , Anti-DDoS( preventing Distributed Denial of Service attacks) , Anti-phishing and fraud prevention and Managed Security services.
The Device Management Service is available in a tiered ‘pay as you use’ structure incorporating:
• Device inventory: know what you’ve got and where it is
• Application management: update, remove and review software across devices
• Capability control: enable or disable functions or capabilities on devices
• Advanced security: keep your data safe with encryption, password management and firewall
The good news for operators is that it is not too late to join the race.A Telco’s success in generating revenues as Identity Brokers depends on upon a close alignement with Enterprise verticals such as Healthcare , Finance and Goverment. With their many assets, operators are in a very good position to take a leading position in the Internet value chain. The operator can also act as “ Trusted Identity Guardian “ for end users and as part of a larger commercial ecosystem.
Sadiq Malik ( Telco Strategist )